Introduction: The Foundation of Digital Trust
In the modern digital economy, data is the most valuable asset an organization possesses. Whether it is a database full of user passwords, a proprietary algorithm, or a stream of financial transactions, data is constantly under threat from malicious actors. To protect this information, software engineers and security architects rely on cryptography—the mathematical science of scrambling data so that it becomes completely unreadable to anyone except authorized parties.
While the underlying mathematics of modern encryption are staggeringly complex, the practical application of cryptography in software engineering boils down to two primary paradigms: Symmetric and Asymmetric encryption. Understanding the architectural differences between these two approaches, and knowing exactly when to deploy them, is the fundamental basis for securing data both when it is sitting on a hard drive (Data at Rest) and when it is traveling across the internet (Data in Transit).
Asymmetric Cryptography: Solving the Distribution Problem
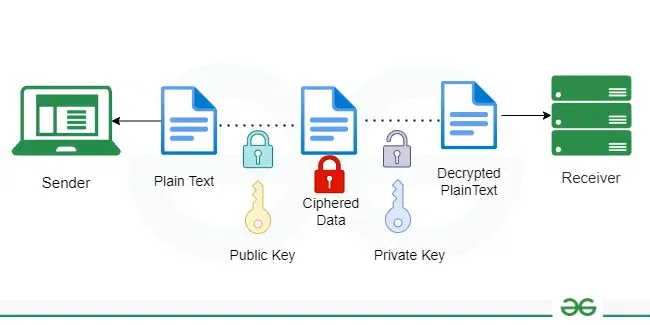
To solve the key distribution problem, cryptographers in the 1970s developed Asymmetric Cryptography (also known as Public-Key Cryptography). Instead of a single shared key, this system generates a mathematically linked key pair: a Public Key and a Private Key.
The fundamental rule of asymmetric cryptography is this: Data encrypted with the Public Key can only be decrypted by the corresponding Private Key.
- The Public Key: This key is completely public. You can post it on your website, email it to strangers, or broadcast it on social media.
- The Private Key: This key is kept absolutely secret and never leaves your server.
If a user wants to send a secure message to your server, they grab your Public Key and use it to encrypt the data. Even if a hacker intercepts the message, they cannot decrypt it—and ironically, once the user encrypts the message, even the user cannot decrypt it. Only the server, holding the closely guarded Private Key, can unlock the ciphertext.
Hybrid Encryption: Securing Data in Transit (TLS/SSL)
Because Symmetric encryption is fast but hard to share, and Asymmetric encryption is easy to share but incredibly slow, modern internet security uses a hybrid approach. This is the exact architecture behind Transport Layer Security (TLS), which puts the “s” in “https://” and protects almost all Data in Transit.
When you connect to a secure website, a “handshake” occurs:
- Asymmetric Start: Your browser connects to the server and requests its Public Key (contained within its SSL/TLS Certificate).
- Key Generation: Your browser uses a fast random number generator to create a brand new, temporary Symmetric Key (called a Session Key).
- Secure Exchange: Your browser encrypts this new Symmetric Key using the server’s Asymmetric Public Key, and sends it across the internet.
- Symmetric Session: The server receives the package, uses its Asymmetric Private Key to unlock it, and retrieves the Symmetric Session Key.
- Bulk Encryption: Now, both your browser and the server possess the same fast Symmetric Key without anyone else seeing it. They abandon the slow asymmetric math and use the symmetric key (usually AES-256) to encrypt all the actual data (passwords, credit cards, HTML) flowing back and forth for the rest of the session.
Securing Data at Rest
While Data in Transit relies on hybrid TLS handshakes, Data at Rest (data sitting statically on physical hard drives, NVMe arrays, or cloud storage buckets) relies almost exclusively on Symmetric encryption.
When a database writes a row of user data to the disk, it encrypts it using AES. However, a new problem emerges: where do you safely store the symmetric key that encrypts the hard drive? If you store the key on the same hard drive as the encrypted data, a hacker who steals the server gets both the lock and the key.
This introduces the concept of Key Management Systems (KMS) and Envelope Encryption. In a modern cloud architecture, the primary symmetric key (the Data Encryption Key, or DEK) is itself encrypted by a master key (the Key Encryption Key, or KEK). The KEK is locked away in a dedicated, highly secure hardware module (HSM) separate from the database. When the database needs to read the disk, it must ask the HSM to temporarily decrypt the DEK, adding a robust layer of isolation and access control.
Conclusion: The Invisible Shield
Cryptography is the invisible shield that protects the global digital economy. Software developers do not usually need to write their own encryption algorithms—in fact, “rolling your own crypto” is widely considered a catastrophic security error. Instead, developers must intimately understand the architecture of these systems. By knowing how to properly leverage the speed of symmetric ciphers alongside the security of asymmetric key distribution, engineering teams can build platforms that guarantee data privacy, integrity, and trust.